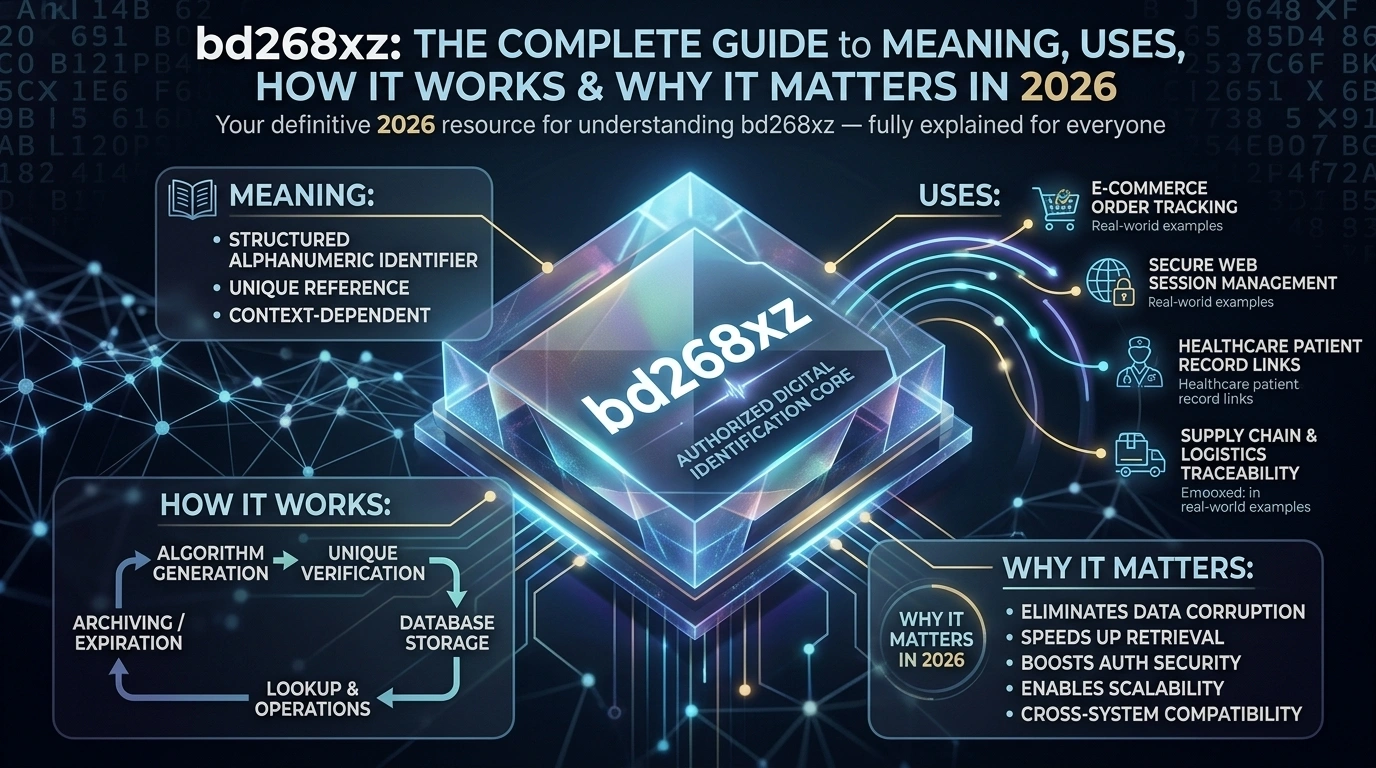
bd268xz: The Complete Guide to Meaning, Uses, How It Works & Why It Matters in 2026
At first glance, a code like bd268xz may seem like a meaningless jumble of letters and numbers. You might have stumbled across it in a software log, on a product label, inside a tracking system, or through an online search — and wondered what it actually means. You are not alone. Thousands of people search for bd268xz every month, often because they encountered it unexpectedly and need to understand its significance.
The truth is that alphanumeric codes like bd268xz are far more important than they appear. In today’s data-driven world, these compact combinations of letters and digits serve as the backbone of digital systems everywhere — from e-commerce platforms and inventory databases to cybersecurity authentication and software development pipelines. Understanding what bd268xz is, how it works, and where it appears is increasingly valuable knowledge for professionals and everyday users alike.
This guide is the most comprehensive resource available on the topic of bd268xz. Whether you are a developer, a business owner, a logistics manager, a student, or simply a curious internet user, this article will give you a clear, thorough, and practical understanding of bd268xz — its meaning, its applications, its benefits, its challenges, and its future. Let us start from the beginning.
What Is bd268xz?
bd268xz is an alphanumeric identifier — a structured string made up of both letters and numbers — that serves as a unique reference code within digital and physical systems. While the string itself may appear random, codes structured like bd268xz are almost always deliberately generated through algorithms or defined by system designers to serve a specific purpose.
The term ‘alphanumeric’ refers to any combination of the 26 letters of the English alphabet (both uppercase and lowercase) and the digits 0 through 9. By blending these two character sets, systems can produce an enormous number of unique combinations. A seven-character alphanumeric code like bd268xz, for example, can represent billions of distinct values — making it an extremely powerful tool for unique identification.
In simple terms, think of bd268xz as a digital fingerprint. Just as no two fingerprints are identical, no two properly generated alphanumeric codes in a well-designed system should be the same. This uniqueness is precisely what makes codes like bd268xz so valuable across dozens of industries and use cases. Without them, managing large volumes of data, products, users, and transactions would become chaotic and error-prone.
It is also important to note that bd268xz does not have a single, fixed meaning that applies universally. Its meaning and function depend entirely on the context in which it appears. In one system it may be a product serial number; in another, a session token; in yet another, an internal document reference. This context-dependence is a defining characteristic of all alphanumeric identifiers.
History and Background of bd268xz
To truly appreciate why codes like bd268xz exist and why they matter today, it helps to understand how alphanumeric identification systems evolved over time. The story begins long before the internet era and traces back to the earliest days of organized data management.
In the mid-20th century, as organizations began managing increasingly large volumes of records — from medical files and financial accounts to government registries and inventory lists — human-readable labels quickly became inadequate. Descriptive names were too long, prone to duplication, and difficult for early computing systems to process efficiently.
The development of ASCII (American Standard Code for Information Interchange) in 1967 was a landmark moment. ASCII provided a standardized way to represent letters and numbers as binary data that computers could process. This created the technical foundation that made alphanumeric codes like bd268xz both possible and practical in digital environments.
Through the 1980s and 1990s, as databases grew in complexity and scale, the need for compact, unique, machine-readable identifiers became critical. Developers began creating automated algorithms — such as UUID (Universally Unique Identifier) generators and hash functions — that could produce codes like bd268xz on demand, guaranteeing uniqueness across massive datasets.
The explosion of the internet in the 2000s accelerated this trend dramatically. E-commerce platforms needed to track millions of products and orders. Web applications needed to manage session IDs, authentication tokens, and API keys. Supply chains needed to trace goods from factory floor to consumer doorstep. All of these requirements are served by precisely the kind of compact, structured alphanumeric code that bd268xz represents.
Today, in 2026, codes like bd268xz are embedded in virtually every digital system on the planet. They are generated millions of times per second across global networks and are the invisible infrastructure that keeps modern data management accurate, secure, and scalable.
How bd268xz Works: A Step-by-Step Explanation
Understanding how a code like bd268xz is generated, assigned, and used helps demystify the entire concept. Here is a clear, step-by-step breakdown of how alphanumeric identifiers like bd268xz function in real-world systems:
Step 1 — The Need for Identification Is Recognized
Every system that uses a code like bd268xz starts with a fundamental requirement: something needs to be uniquely identified. This could be a product arriving at a warehouse, a new user registering on a platform, a file being created in a database, or a session being initiated in a web application. The moment this object or event comes into existence, the system recognizes the need to assign it a unique reference.
Step 2 — The Algorithm Generates the Code
A code generation algorithm — which could be a random number generator, a hash function, a UUID generator, or a custom encoding scheme — produces the alphanumeric string. In the case of bd268xz, the algorithm likely draws from a pool of lowercase letters (b, d) and digits (2, 6, 8) combined with additional characters (x, z) in a pattern that maximizes uniqueness while keeping the code compact and processable.
Step 3 — Uniqueness Is Verified
Before the code is officially assigned, the system typically checks its database to confirm that bd268xz has not already been used. In large-scale systems, this is done automatically and near-instantaneously. If a duplicate is detected (which is extremely rare with well-designed algorithms), a new code is generated and checked again.
Step 4 — The Code Is Assigned and Stored
Once verified as unique, bd268xz is assigned to its target — the product, user, session, or file — and stored in the system’s database alongside relevant metadata. This metadata might include the creation timestamp, the associated user or entity, status information, and expiration settings if applicable.
Step 5 — The Code Is Used for Lookup and Operations
From this point forward, bd268xz serves as the primary reference for its assigned entity. When a system or user needs to retrieve, update, track, or verify the entity, they use bd268xz as the lookup key. This is faster and more reliable than searching by descriptive name or other variable attributes.
Step 6 — The Code Expires or Is Archived (Where Applicable)
Depending on the system design, bd268xz may remain active indefinitely (as in a permanent product serial number) or expire after a defined period (as in a one-time verification token or session ID). Upon expiration, the code is either deleted or archived, freeing up system resources while maintaining an audit trail.
Key Features of bd268xz as an Alphanumeric Identifier
What makes a code like bd268xz so effective and widely adopted across industries? Here are the most important features that define alphanumeric identifiers of this type:
1. High Uniqueness Capacity
A seven-character alphanumeric string like bd268xz can represent over 78 billion unique combinations when using just lowercase letters and digits. In systems that also include uppercase letters, this number grows to over 3.5 trillion. This enormous combination space makes duplication practically impossible in even the largest databases.
2. Compact and Efficient
Unlike descriptive labels that might require dozens of words to convey meaning, bd268xz conveys complete identification in just seven characters. This compactness makes it ideal for storage, transmission, display on labels and barcodes, and processing by automated systems.
3. Machine-Readable and System-Agnostic
Codes like bd268xz can be processed by virtually any programming language, database system, or platform. They fit naturally into APIs, query strings, JSON data structures, barcodes, QR codes, and database primary keys — making them universally compatible across technical environments.
4. Unpredictable and Secure
Because bd268xz does not follow a predictable pattern visible to outside observers, it adds a meaningful layer of security when used for tokens, verification codes, or access keys. It is significantly harder to guess than sequential numeric IDs or human-chosen passwords.
5. Context-Flexible
The same structural format used by bd268xz can serve completely different purposes in different systems. This flexibility means that a single code design approach can be applied across inventory management, user authentication, document control, logistics tracking, and many other domains.
6. Audit Trail Compatible
Because bd268xz is unique and persistent, it can be used to build complete audit trails. Every action taken on the entity associated with bd268xz — creation, modification, transfer, deletion — can be logged against this identifier, creating a traceable history that is invaluable for compliance, debugging, and dispute resolution.
Benefits of Using Codes Like bd268xz
Organizations and systems that adopt alphanumeric identifiers like bd268xz gain a wide range of practical advantages. Here are the most significant benefits:
- Eliminates Duplicate Records: Because each bd268xz-style code is unique, it prevents the data corruption and operational errors that arise when two records share the same identifier.
- Speeds Up Data Retrieval: Searching a database by a compact alphanumeric key like bd268xz is dramatically faster than searching by descriptive text fields, especially in large datasets with millions of entries.
- Enhances Security: In authentication and verification contexts, the unpredictability of bd268xz makes unauthorized access significantly more difficult than with sequential or pattern-based identifiers.
- Supports Automation: Automated systems — from warehouse robots to API workflows — process alphanumeric codes like bd268xz with perfect accuracy and at machine speed, reducing human error.
- Improves Scalability: As a system grows from thousands to millions of records, the combination space of bd268xz-style codes ensures the identification system scales seamlessly without redesign.
- Enables Cross-System Integration: When multiple platforms need to share data about the same entity, a shared identifier like bd268xz provides a reliable common reference that every system can use.
- Simplifies Compliance and Auditing: Regulatory requirements in industries like healthcare, finance, and logistics often demand traceable records. Unique codes like bd268xz make compliance documentation straightforward.
- Reduces Storage Overhead: A compact seven-character string requires minimal storage space compared to descriptive labels, improving database efficiency especially at scale.
- Works Across Physical and Digital Systems: bd268xz can be printed on a physical label, encoded in a barcode, stored in a database, and transmitted via API — bridging the gap between the physical and digital worlds seamlessly.
- Future-Proof by Design: The mathematical properties of alphanumeric identifiers like bd268xz ensure they remain viable identification tools regardless of how technology evolves.
Real-World Examples of bd268xz in Action
Abstract concepts become clearest through concrete examples. Here are four real-world scenarios that illustrate exactly how a code like bd268xz functions in practice:
Example 1: E-Commerce Order Tracking
An online retailer processes tens of thousands of orders every day. When a customer places an order, the system immediately generates a unique alphanumeric code — for instance, bd268xz — and assigns it to that specific order. This code appears on the confirmation email, the shipping label, the warehouse picking list, and the delivery notification. At every stage of the fulfillment journey, staff and automated systems use bd268xz to locate, update, and verify the order’s status. Without this unique identifier, tracking a specific order among thousands would be an error-prone, time-consuming nightmare.
Example 2: Software Session Management
When a user logs into a web application, the server generates a session token — an alphanumeric code like bd268xz — and stores it as a cookie in the user’s browser. Every subsequent request from that browser includes bd268xz as proof of the active session. The server validates this token before serving any protected content. When the user logs out or the session expires, bd268xz is invalidated. This mechanism is fundamental to how almost every login-protected website on the internet manages user authentication securely.
Example 3: Healthcare Patient Record Management
A hospital system assigns each patient a unique alphanumeric identifier — such as bd268xz — upon registration. This code links together all records associated with that patient: lab results, prescription history, imaging files, appointment records, and billing information. Even if the patient’s name changes (through marriage, for example) or if their records are transferred to a different facility, bd268xz remains a stable, consistent reference that prevents records from being mixed up or lost. In healthcare, where accuracy can literally mean the difference between life and death, this kind of reliable identification is mission-critical.
Example 4: Supply Chain and Logistics Management
A global manufacturer ships thousands of product batches each month to distributors across multiple countries. Each batch is assigned a unique identifier like bd268xz at the point of production. This code is encoded in a barcode or QR code that travels with the batch throughout the supply chain. At customs checkpoints, distribution centers, and retail receiving docks, scanning bd268xz instantly retrieves the full provenance of that batch — including production date, factory location, ingredients or components, and quality control results. If a product recall is ever necessary, bd268xz makes it possible to identify and isolate the specific affected batch within minutes rather than days.
Comparison Table: bd268xz vs. Other Identifier Types
How does a code like bd268xz compare to other common methods of identification used in digital and physical systems? The table below provides a clear side-by-side comparison:
| Feature | bd268xz Style | Sequential ID | UUID | Barcode (EAN) | QR Code | Plain Name |
| Uniqueness | Very High | High | Extremely High | High | High | Low |
| Compactness | Excellent | Good | Poor (36 chars) | Good | Good | Poor |
| Security | Good | Low | Excellent | Moderate | Moderate | Very Low |
| Human Readable | Moderate | Good | Poor | Poor | None | Excellent |
| Machine Readable | Excellent | Excellent | Excellent | With scanner | With scanner | Poor |
| Scalability | Excellent | Good | Excellent | Good | Good | Poor |
| Cross-System Use | Excellent | Moderate | Excellent | Limited | Limited | Poor |
| Generation Speed | Fast | Fast | Fast | Requires device | Requires device | Manual |
Common Problems and Challenges with Codes Like bd268xz
Despite their many advantages, alphanumeric identifiers like bd268xz are not without challenges. Understanding these limitations helps organizations plan and manage their identification systems more effectively:
1. Loss of Context Without Documentation
The biggest risk with a code like bd268xz is that it carries no inherent meaning. If the documentation linking bd268xz to its assigned entity is lost, corrupted, or inaccessible, the code becomes useless. Organizations must maintain rigorous documentation practices to ensure that every identifier remains interpretable throughout its lifecycle.
2. Visual Confusion Between Similar Characters
Some alphanumeric characters look very similar to one another — the letter ‘b’ can resemble ‘6’, while ‘x’ and ‘z’ may be confused in certain fonts. When codes like bd268xz are displayed in print or on screens with poor font choices, these visual ambiguities can lead to transcription errors. Best practice is to use clear, monospace fonts and, where possible, to exclude visually ambiguous characters from code generation pools.
3. Collision Risk in Poorly Designed Systems
While the theoretical combination space of bd268xz-style codes is vast, poorly designed generation algorithms can produce collisions — cases where the same code is assigned to two different entities. Without robust uniqueness-checking mechanisms, this can cause serious data integrity problems. Well-designed systems include collision detection as a mandatory step in the code assignment process.
4. Dependency on System Accuracy
A code like bd268xz is only as useful as the system that manages it. If the database storing the link between bd268xz and its entity is poorly maintained, migrated incorrectly, or corrupted, the identifier becomes orphaned — pointing to nothing. Regular database audits and backup procedures are essential safeguards.
5. User Confusion and Resistance
Non-technical users who encounter bd268xz in interfaces — such as on invoices, receipts, or confirmation pages — may find it confusing or alarming. Organizations should accompany alphanumeric identifiers with clear labels (e.g., ‘Your Order Reference: bd268xz’) to ensure users understand what the code represents and why it matters.
6. Security Risks If Exposed Inappropriately
In contexts where bd268xz serves as an authentication token or access key, its exposure in logs, URLs, or error messages creates security vulnerabilities. Codes used for sensitive purposes should be treated as confidential data, transmitted only over encrypted channels, and never logged in plain text.
Tips for Using Codes Like bd268xz Effectively
Whether you are a developer implementing an identification system, a business owner managing inventory, or a user trying to make sense of an unfamiliar code, these practical tips will help you work with bd268xz-style identifiers more effectively:
- Always Record Context Alongside the Code: Whenever bd268xz is generated or referenced, ensure the system also records what it refers to, when it was created, and in what context. A code without context is just noise.
- Use Clear, Legible Typography: If bd268xz appears on printed materials, labels, or user interfaces, choose fonts that clearly distinguish similar characters. Monospace fonts like Courier or Consolas are ideal for displaying alphanumeric codes.
- Validate Format Before Processing: Before acting on any code that claims to be in the bd268xz format, validate its length and character composition programmatically. Reject inputs that do not match the expected pattern to prevent injection attacks and data errors.
- Never Reuse Expired Codes: Even after bd268xz has expired or its associated entity has been deleted, resist the temptation to reassign the same code to a new entity. This prevents historical confusion and maintains audit trail integrity.
- Implement Checksum Verification Where Appropriate: For high-stakes applications — such as financial transaction IDs or medical record numbers — add a checksum character to bd268xz-style codes. This allows automatic detection of single-character transcription errors.
- Educate End Users About What the Code Means: If users see bd268xz on a confirmation page or receipt, provide a brief explanation such as ‘Save this reference number to track your order.’ This prevents confusion and unnecessary support inquiries.
- Store Codes as Text, Not Numbers: Even though bd268xz contains digits, always store it as a text (string) field in databases rather than a numeric field. Numeric storage can strip leading zeros or interpret the string incorrectly.
- Log Code Usage for Audit Purposes: Every time bd268xz is used — whether to retrieve a record, authenticate a session, or authorize a transaction — log that usage event. These logs are invaluable for debugging, compliance audits, and fraud investigation.
The Future of bd268xz and Alphanumeric Identification
The role of alphanumeric codes like bd268xz in our digital infrastructure is not diminishing — it is growing. As technology evolves across multiple fronts, the importance and sophistication of these identifiers continue to increase. Here are the key trends shaping the future of bd268xz-style codes:
Artificial Intelligence and Machine Learning Integration
AI systems increasingly depend on unique identifiers to track training data, model versions, experiment runs, and inference requests. In the AI era, codes like bd268xz are becoming essential infrastructure for managing the massive scale and complexity of machine learning pipelines. Systems like MLflow, Weights & Biases, and similar platforms already rely heavily on alphanumeric run identifiers analogous to bd268xz.
Internet of Things (IoT) Explosion
The global IoT ecosystem is projected to include tens of billions of connected devices by the end of this decade. Every smart sensor, connected appliance, industrial machine, and wearable device requires a unique identifier. Codes structured like bd268xz are ideal for this purpose — compact enough to store on low-memory devices, yet unique enough to manage at planetary scale.
Blockchain and Decentralized Identification
Blockchain technology uses cryptographic hash functions to generate identifiers that share structural similarities with codes like bd268xz. As decentralized identity systems (DIDs) gain adoption, the principles underlying bd268xz-style codes are being extended into self-sovereign identity frameworks that give individuals control over their own digital identifiers.
Zero-Trust Security Architectures
In zero-trust security models, every access request must be verified continuously rather than assumed to be safe once inside a network perimeter. This drives increasing demand for sophisticated, short-lived alphanumeric tokens analogous to bd268xz — generated freshly for each interaction and invalidated immediately upon use.
Quantum-Resistant Identification
As quantum computing advances, traditional cryptographic methods may become vulnerable. The cryptographic community is developing new identifier generation methods that remain secure in a post-quantum world. These next-generation codes will likely maintain the compact, alphanumeric structure exemplified by bd268xz while incorporating quantum-resistant mathematical properties.
The trajectory is clear: codes like bd268xz are not a legacy technology on their way out. They are evolving, adapting, and becoming more central to digital infrastructure with every passing year. Understanding them today is an investment in digital literacy that pays dividends well into the future.
Frequently Asked Questions About bd268xz
Q1: What exactly is bd268xz?
bd268xz is a seven-character alphanumeric identifier — a code made up of letters and numbers — that is used to uniquely reference a specific entity within a digital or physical system. It has no single universal meaning; its purpose depends entirely on the context in which it appears. In one system, bd268xz might be a product tracking code; in another, a session token or internal document reference.
Q2: Why do so many people search for bd268xz online?
People search for bd268xz because they have encountered it unexpectedly — on a confirmation email, in a software error log, on a product label, or through a shared link — and want to understand what it means. Because alphanumeric codes carry no inherent human-readable meaning, encountering one naturally prompts curiosity. This guide exists specifically to answer that curiosity comprehensively.
Q3: How does bd268xz work in a technical system?
In a technical system, bd268xz is generated by an algorithm, checked for uniqueness against existing records, assigned to a specific entity (such as a user, product, or session), and stored in a database. From that point forward, bd268xz serves as the primary lookup key for that entity — enabling fast, accurate retrieval, tracking, and management of the associated data.
Q4: Is bd268xz safe?
bd268xz itself is a neutral identifier — it is neither inherently safe nor unsafe. Its safety implications depend entirely on context. When used as a session token or authentication code, it should be treated as sensitive data: transmitted over encrypted connections, not logged in plain text, and invalidated promptly when no longer needed. When used as a non-sensitive product tracking code, standard data management practices are sufficient.
Q5: Who should understand how bd268xz works?
Anyone who works with digital systems, data management, software development, e-commerce, logistics, healthcare records, or cybersecurity will benefit from understanding how codes like bd268xz function. Additionally, everyday users who encounter these codes on invoices, confirmation pages, or product labels will find this knowledge helpful for interpreting what they see and protecting their own data.
Q6: What are the main benefits of using a code like bd268xz?
The main benefits include guaranteed uniqueness across large datasets, compact size for efficient storage and processing, machine-readability for automation compatibility, unpredictability for security applications, and flexibility to serve multiple purposes across different system types. These advantages make bd268xz-style codes the preferred identification method in virtually every modern digital system.
Q7: Is the use of codes like bd268xz growing?
Yes, absolutely. As the volume of digital data, connected devices, and automated systems continues to grow exponentially, the demand for reliable unique identifiers like bd268xz is increasing in parallel. Every new IoT device, every new database record, every new user account, and every new blockchain transaction requires a unique identifier. The structural approach represented by bd268xz is more relevant and widely used in 2026 than it has ever been before.
Q8: How can I tell what bd268xz means in a specific context?
To determine what bd268xz means in your specific situation, follow these steps: identify the platform or system where you encountered it; check whether it is associated with a confirmation, error, or tracking notification; search the platform’s help documentation for information on reference codes; and if unclear, contact the system’s support team with bd268xz as your reference. Context is everything when interpreting alphanumeric identifiers.
Conclusion
bd268xz may be just seven characters long, but what those seven characters represent is far greater than their appearance suggests. As this guide has shown, codes like bd268xz are the invisible infrastructure of modern digital life — quietly managing the uniqueness, security, and traceability of billions of records, products, users, and transactions around the world every single day.
From its origins in the early days of computing to its central role in today’s AI-powered, IoT-connected, blockchain-enabled world, the alphanumeric identifier exemplified by bd268xz has proven itself to be one of the most enduring and versatile tools in the digital toolkit. It is compact, unique, machine-readable, secure, and infinitely scalable.
Whether you encountered bd268xz in a software log, on a shipping label, in a verification email, or through an online search, you now have the complete picture. You understand what it is, how it is generated, where it is used, why it matters, and how to work with it effectively. That knowledge is genuinely valuable in an increasingly data-driven world.
The next time you see bd268xz — or any code like it — you will not be left wondering. You will recognize it for what it is: a precisely designed, purposeful identifier doing an important job quietly and efficiently behind the scenes of the digital world you navigate every day.